I feel I’ve always known that things on the internet will get discovered eventually. Many years ago, I took my first foray into self-hosting. A discarded Windows PC became a Linux host, the Linux machine became a local network server allowing multiple machines to be online at once. And with the dedicated phone line, it kept the connection alive even while we slept. As my curiosity grew, I began hosting all the things; a simple website, a photo gallery, an email server, a shared calendar, and even my own attempt at an LDAP backed address book that worked with Nokia phones.
There were risks of course. Spam was the biggest one. But defensive tools were just as exciting as the software I wanted to host. I explored gray-listing, filesystem change detection, fail-to-ban, obscure port knocking sequences that would open up a hole in the firewall to allow an SSH connection in. It was a great time to explore. But the risk remains. By making a service available on the internet, it becomes discoverable on the internet. If it is discoverable, bad actors are going to try and exploit it. Within hours of a machine being exposed to the internet, you could be sure someone would try to get in. Often these were brute force attempts at SSH passwords for common usernames. For websites, there was the constant search for PHP vulnerabilities or admin pages.
Some of you may dismiss this post as blindingly obvious. Surely the message that nothing is safe on the internet has sunk in by now. But no, the desire for convenience is strong. Whether you want to share a service with a colleague, expose your HomeAssistant instance outside the home, or give yourself access to whatever agentic tool is popular today, the temptation to put things on the internet is everywhere. It is not only tempting but it is easier than ever to do. Start something that listens on a port in VSCodium with the Tailscale plugin and you are invited to make it available on the internet.
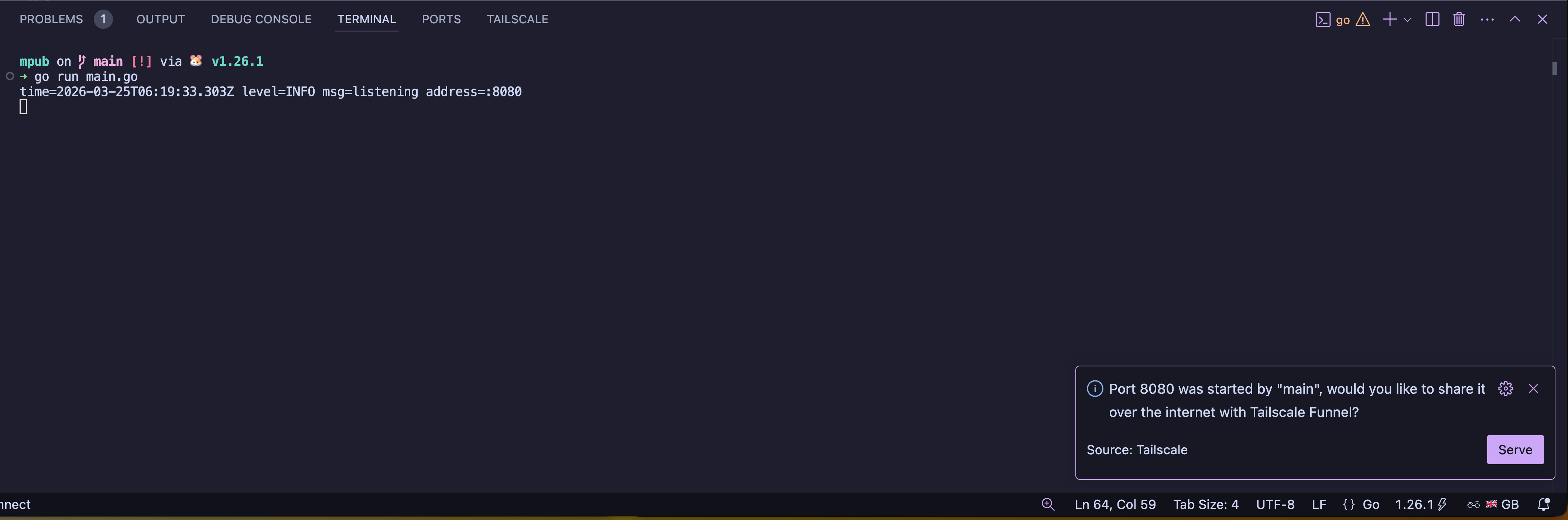
Would you like to expose yourself to the world?
This is incredibly useful and is one of the reasons I use the plugin, but it is not without risk. Now to be fair to Tailscale, the Funnel service is not available by default. I need to enable it and grant my user/machine permission to use Funnel.
Yesterday I was building a simple Micropub server that would allow me to post to my blog from iA Writer. Mac OS sandboxing meant that I couldn’t use a localhost URL in iA Writer for my Micropub server. I took advantage of the VSCodium integration with Tailscale and hit the helpful little “Funnel” button in the popup that appeared when I started the server. My service was live to the world.
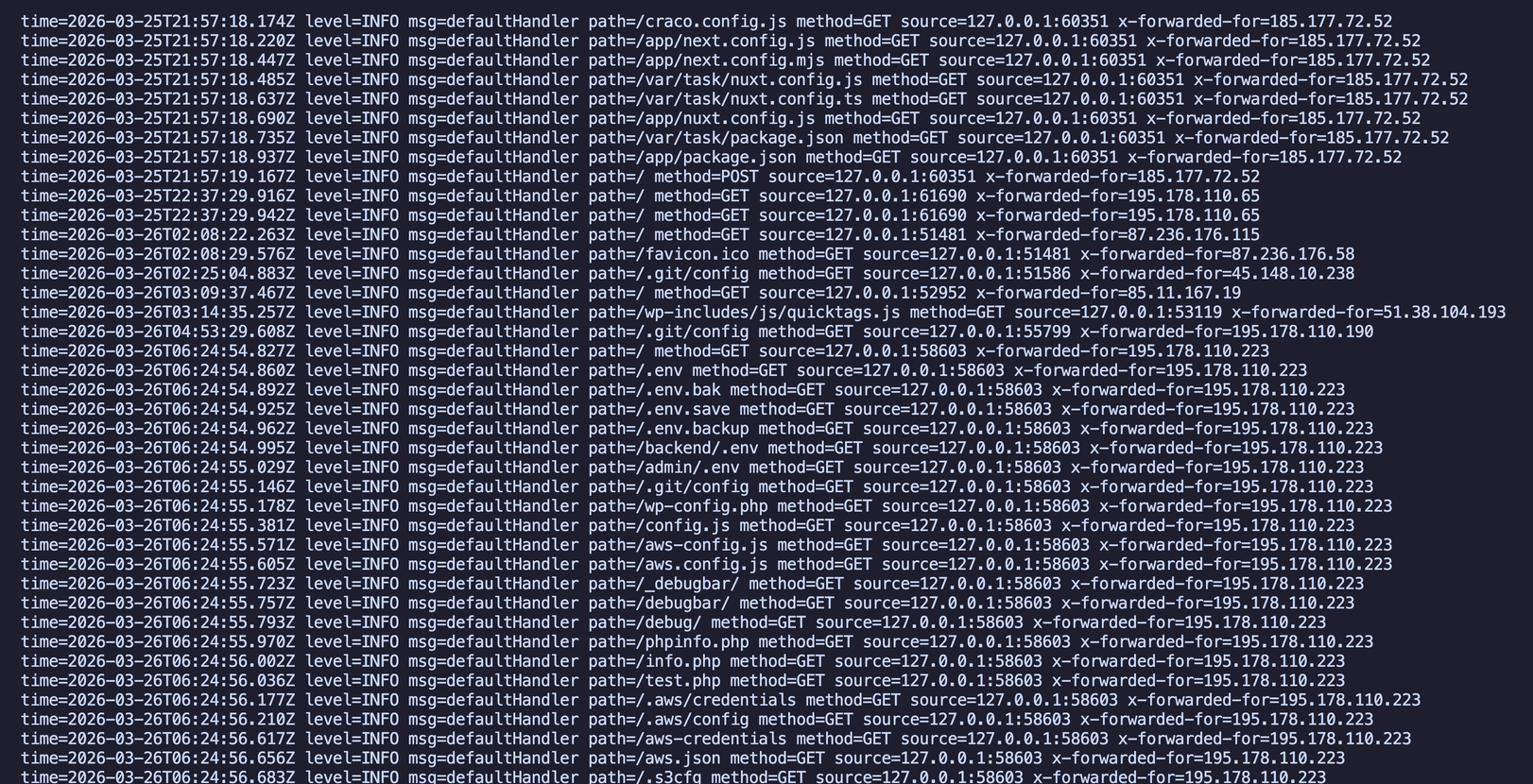
Automated attempts to probe for vulnerable software.
Within seconds the logs started to pour in with attempts to extract environment variables, secrets, git history. If I’d slipped up and not constrained my server to respond to only a small handful of defined paths then the contents of secrets, perhaps stored in a .env file could have been gone within seconds.
What I hadn’t appreciated was just how quickly this scanning can happen. You have to assume that your service will be discovered within minutes and not hours.
“On a computer with a gigabit connection, ZMap can scan the entire public IPv4 address space on a single port in under 45 minutes. With a 10gigE connection and PF_RING, ZMap can scan the IPv4 address space in 5 minutes.” – The ZMap Project
Now imagine there are more than one of these scanners running. The time to discovery goes down dramatically as the number of scanners increases. A GreyNoise look at scanning by legitimate actors in 2024 showed that a service could expect to be identified within five minutes of coming online. I can only assume that bad actors are scanning equally frequently, if not more so.